Office of Research and Sponsored Programs
Research Security
Reporting a Research Security Concern
Any issues related to research security should be promptly reported to the Research Compliance Office. Upon receipt of a research security concern, the Research Compliance Officer will immediately be reported to the Chief Information Security Officer (CISO) for review. If, upon review of the reported issue, the CISO determines an incident has occurred, the CISO will follow the MTSU Cyber Incident Response Plan (CIRP). If no incident has occurred the CISO and Research Compliance Team may choose to appoint an investigative committee comprised of three (3) faculty and/or staff from outside the department of the reported issue and the Research Compliance Team to investigate and propose preventative processes to address the future occurrence of the issue.
Research Security Training Requirements
Many federal agencies are requiring completion of research security training. This table provides an overview of the effective date and completion requirements for those agencies.
| Federal Agency | Effective Date | Who’s required to take the training? | How often do I need to take the training? |
|---|---|---|---|
| DOE | May 1, 2025 | PI, PD, Co-PI, Co-PD, project manager, any individual functionally performing as a PI, PD, Co-PI, Co-PD, or project manager. DOE may expand this list as specified in NOFO and/or terms and conditions of the Federal financial assistance award | Within the 12 months prior to the application submission New personnel must complete training within 30 days of joining the project |
| NSF | December 2, 2025 | All senior/key personnel | Within the 12 months prior to application submission |
| USDA | December 31, 2025 | All individuals employed by the recipient to work on the award | Within the 12 months prior to the application submission Recertified annually for the duration of the award |
| NIH | May 25, 2026 | All senior/key personnel listed on the grant application | Within the 12 months prior to the application submission |
| NASA | August 5, 2026 | Any Principal Investigator (PI) or Co-PI (regardless of level of effort), and Co-Investigators (Co-I) proposing to spend 10% or more of their time in any given year on the NASA-funded award. | Within the 12 months prior to the application submission |
For more information on the research security training requirements for a particular agency, visit the links below.
DOE: Research Security Training Requirement | Department of Energy, Research Security Training Requirements for all R&D Financial Assistance Awards
NSF: Updates to NSF Research Security Policies
USDA: Current USDA General Terms and Conditions for Federal Awards
NIH: Research Security Training Requirements for NIH
NASA: GIC 26-02: Research Security Training Requirements
Completing the Required Training
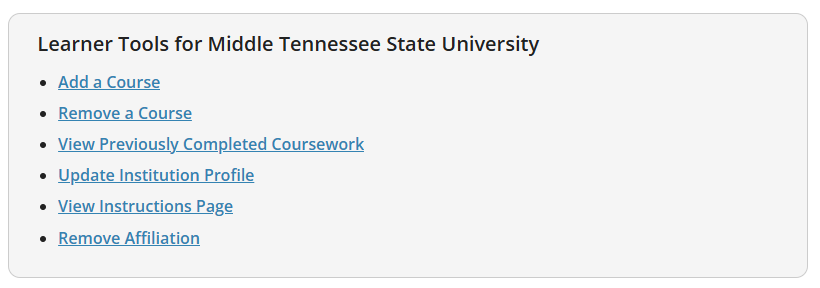
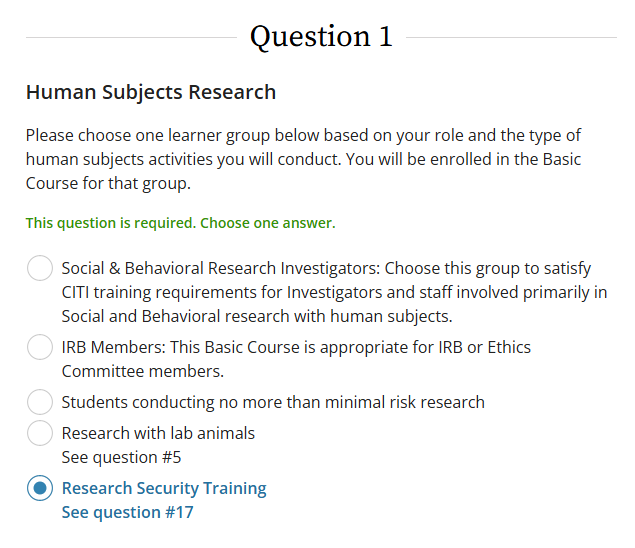
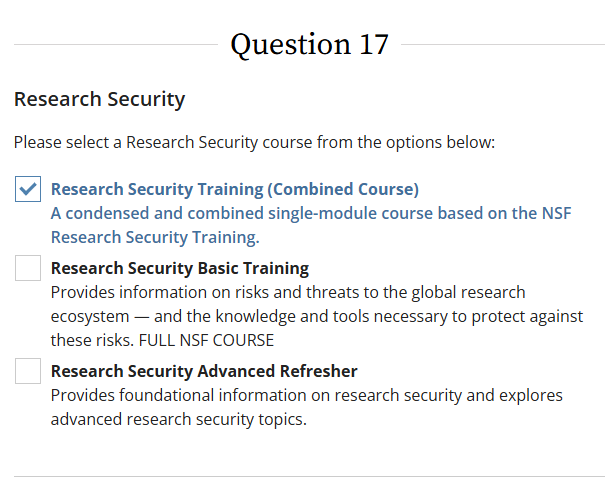
MTSU offers the required training through CITI Program. To add the course to your account, use the Learner Tools box at the bottom of the page to enter the Add a Course questionnaire. You will need to answer questions 1 & 17 to add the required research security course to your account.
Once completed, download the completion certificate(s) and upload them to your Cayuse grant proposal application as required. This includes the completion certificates for any other senior/key personnel who are listed on the grant proposal.
Contact Information
Research Compliance Office
615-494-8751
Deb Zsigalov
Chief Information Security Officer
615-898-2036
Related Policies
Research Security Policy: https://www.mtsu.edu/policies/407-mtsu-research-security/
Export Control Policy: https://www.mtsu.edu/policies/p080/
Information Security Policy: https://www.mtsu.edu/policies/p920/
Information Technology Resources: https://www.mtsu.edu/policies/p910/

